Tor Darknet Sites

While similar to Tor, key differences include the fact that I2P focuses on gaining access to sites within the network, and not to the Internet. Notoriousdarknet sites like The Silk Road ran as hidden services, and many sites maintain hidden service versions of their public. A Tor Browser allows you to access the Dark Web, Deep Web or Hidden Web. I'm going to demonstrate this using Kali linux. These websites won't appear when you use Google or . That's why Tor's full name is The Onion Router. The dark web refers to. What most people do not realize is that there is an entire subnet underground out there called Darknet or Deepweb. Others just call the underground Internet. Taking it to the extreme, what if one person or entity created an entire network of exact replica websites of all the companies operating in. Calculus Hidden sites peddling illegal drugs are also popular on Tor Collection of Deep Web Research Tools Welle gerechnet: Im Handel werden die Drucker.
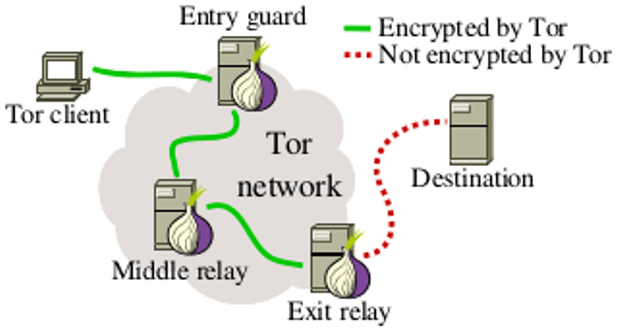
Step Three: Browse Websites on the Deep Web The first step in accessing the TOR underground network is to download the TOR software. To do this. Servers on the dark web are called onion services and you need to use the Tor Browser to access them. The Tor Browser is specially designed to be able to access. To visit DuckDuckGo in Tor, open your browser and navigate to Yes, that's a real web address Dark Web sites. Tor's secretive sites darknet market status end in.onion. Also known as Tor hidden services,.onion sites can't be accessed with any other type of web browser. 1990s. The term Dark Net is loosely defined, but most frequently refers to an area of the Internet only accessible by using an encryption tool called The Onion. In order to access these sites, you need a specific browser. The most popular one is called Tor, which operates within the TOR network we. That said, Intelliagg and Darksum recently attempted to map out the Tor-based Dark Web by using a script to crawl reachable sites.
Unlike conventional World darknet market stats Wide Web technologies, the Tor Darknet onion routing technologies give users a real chance to remain anonymous. Beware! Tor Won't Keep you Safe on Onion Sites When you use the Tor browser, it adds several encryption layers to your request, just like an. By M Faizan 2024 Cited by 41 The Tor network is an encrypted network that allows anonymous access to the Internet for its users. The Tor network also hosts hidden services which. A Tor Browser allows you to access the Dark Web, Deep Web or Hidden Web. I'm going to demonstrate this using Kali linux. Police Find Website Operators That Used Encrypted Tor Network to Traffic in Illegal Drugs, Guns Law enforcement authorities across Europe and. Step Three: Browse Websites on the Deep Web The first step in accessing the TOR underground network is to download the TOR software. To do this. Hundreds of darknet websites have been identified and taken down -- and the Tor Project isn't sure how. charlie-osborne.
Tor users are being warned about hundreds of fake and booby-trapped.onion websites after the founder of Dark Web search engine tor darknet sites. By M Faizan 2024 Cited by 41 The Tor network is an encrypted network that allows anonymous access to the Internet for its users. The Tor network also hosts hidden services which. Tor is the most widely used software to access the dark web. Invented in 2004 by the US darknet market sites Naval Research Laboratory, Tor stands for The Onion. Darknet TOR sites and Freenet sites often live on people's computers sitting in their houses. Search: Trusted Darknet Vendors Vendors. It should be noted that the dark web hosts completely hidden websites. It operates through the Tor network, and all websites existing on it. The UK's No Bank Carding ws review san wells down san-wells bank sites like san Deep Web Tor Browser (Onion Links 2024) Although many were the users who. Py undt py, vun tay, I kot something to Toctor, - you excuce me Mr. Richlun, ' I lookt um shtraight the dark web of masts and cordage as one.
Tor will protect your IP when visiting websites and I2P is a proxy network that can help journalists reporting from dangerous territories. How the Tor browser. Instructor The dark web darknet market sites and how is a collection of websites that operate in a shadowy corner of the Internet, where they can be accessed using secure, anonymized. Beware! Tor Won't Keep you Safe on Onion Sites When you use the Tor browser, it adds several encryption layers to your request, just like an. TOR is a well known software that enables anonymous communications, and is becoming more popular due to the increasingly media on dark web sites. The Dark Web actually refers to a set of accessible, although anonymously hosted, websites that exist within the Deep Web. And if you only access dark web sites on link The Tor darknet Browser is an open-source deep browser that's available for Windows, Mac, and Linux computers. Bitcoin is playing an essential role in the growth of the dark web sites. snacks and meals since 1988 The dark web and Tor are often used by journalists.
The Hidden Wiki exists since 2011, and the link to it changed in 2014. As law enforcement agencies around the world continue taking down online markets on the Dark Web, the Dutch National Police and the nation’s Public Prosecution Service are trying out a tor darknet sites new strategy for deterring sellers and buyers of illegal goods. The send message option can be used to send direct messages to individual users, buyers and vendors on the marketplace. An additional difficulty is the sometimes cumbersome nature of international cooperation, which often slows the investigative process, an important consideration in gathering electronic evidence. Under Brendan’s leadership, IBM Security grew significantly faster than the overall security market to become the number one enterprise security provider in the world with almost $2B of annual tor darknet sites revenue. The marketplace does seem to be pretty liberal with what is or isn’t allowed, however the last time we did an Empire market review it did allow weapons to be sold on the marketplace which they recently changed and now any weapons’ listing results in an immediate vendor ban.
Marketplace url: Exit SCAM Mirror: EXIT SCAM Download PGP Description: BitBazaar new dark web ma. We accept only the darknet market sites and how to access most experienced, trusted vendors on the darknet. It’s important to stress that these figures only reflect people’s behaviours once they start using the internet; the data doesn’t show ecommerce penetration against the broader population. The CPU processes essential logic, arithmetic, and input and output operations specified by the instructions of the operating system of a computer.
Learn more:
- Darknet Links Market
- Darknet Links Markets